New Appinventiv Report Details Critical Biometric Authentication Risks in Enterprise AI Voice Cloning Systems

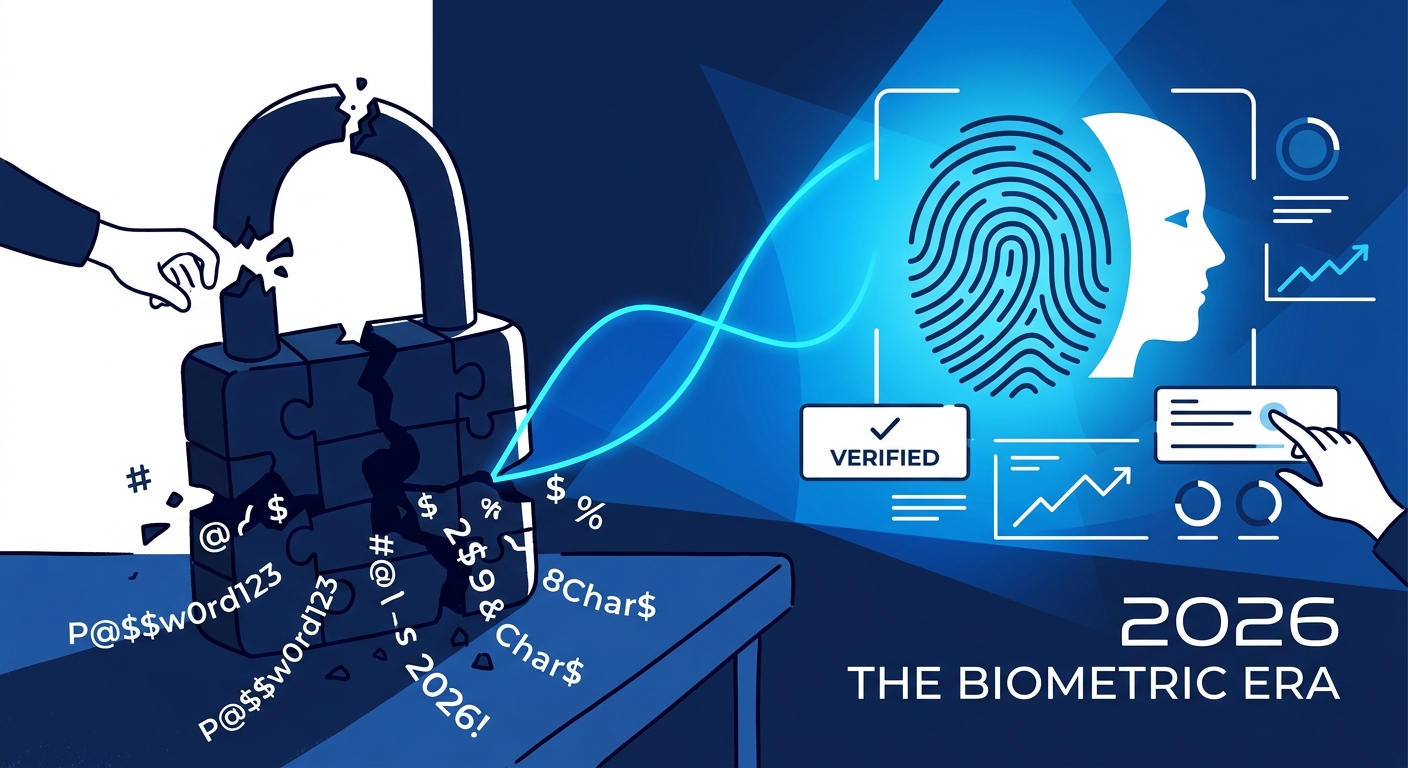
On April 14, 2026, a report titled The State of Biometric Security in the Age of AI Fraud dropped, and it’s a wake-up call for anyone betting the farm on voice AI. We aren't just talking about simple chatbots anymore. We’re talking about autonomous agents—digital workers capable of pulling levers on financial and operational workflows. As these systems move from the fringes to the center of the enterprise, the old-school security measures we’ve relied on are starting to look like paper shields in a gunfight.
The reality? We’ve sprinted toward integration without checking the locks. Synthetic voice fraud—deepfakes, mimicry, the whole nasty bag of tricks—has spiked by over 300% in just a few years. If your security strategy still treats biometric verification as an infallible "get out of jail free" card, you’re already behind the curve.
Right now, 70% of large enterprises are elbow-deep in testing or deploying advanced conversational AI. It’s not just internal, either. Consumers are jumping on board, too; voice-assisted eCommerce has hit $19.4 billion, a fourfold jump in two years. When your voice agent is the gatekeeper for sensitive data and cold, hard cash, you better make sure your voice agent security isn't just a suggestion.
The Five-Layer Security Framework
Perimeter defense is dead. If you’re only guarding the front door, you’ve already lost. The Appinventiv report makes it clear: you need a layered architecture that watches every single move a voice-based request makes throughout its lifecycle.
Think of it as a gauntlet. If a threat slips past one layer, it should hit a wall at the next. Here is how you lock it down:
- Audio Input: This is the front line. You have to harden the capture point against injection attacks and signal tampering before the system even knows what it’s hearing.
- Speech-to-Text (STT): It’s not enough to just transcribe; you have to ensure the process is immune to adversarial inputs designed to trick the model into hearing what it shouldn't.
- LLM Reasoning: This is the brain. You need guardrails that prevent the Large Language Model from being "jailbroken" or manipulated by malicious instructions hidden in the audio stream.
- Text-to-Speech (TTS): The output phase is where impersonation happens. Securing this prevents unauthorized synthesis of your brand or your executives' voices.
- Telephony/API: This is where the rubber hits the road. Hardening the connection points between your AI and your internal databases is the only way to prevent a voice bot from being used as a skeleton key for your backend systems.

Measuring Risk and Performance
The transition to autonomous agents—the kind of AI agents in enterprise that can actually do work—demands a new scorecard. You can’t measure a system that can lie to you or be tricked by a deepfake using the same metrics you used for a static database.
If you aren't tracking these three benchmarks, you’re flying blind:
| Benchmark | Description |
|---|---|
| False Acceptance Rate (FAR) | The frequency at which the system incorrectly verifies an unauthorized user or synthetic voice. |
| Hallucination Rate | The frequency at which the LLM generates inaccurate or unintended information during a transaction. |
| Attack Success Rate | The percentage of adversarial attempts that successfully bypass security controls to execute unauthorized actions. |
The High Stakes of the AI Ecosystem
The risk isn't siloed. Whether you’re deploying AI agents in customer service or building a sophisticated voicebot in banking, the stakes are identical: one successful hack can wipe out your bottom line and torch your reputation overnight.
We need a fundamental shift in how we handle compliance. You can’t just patch this and walk away. It requires continuous monitoring and real-time anomaly detection. Stop treating your voice agents like peripheral tools and start treating them like high-value, high-risk infrastructure.
The efficiency gains of AI are real, but they come with a tax. Synthetic voice fraud isn't a "phase" or a temporary glitch; it’s a permanent feature of the modern digital economy. If you’re operating at scale, a multi-layered defense strategy and rigorous, measurable security benchmarks aren't just "best practices"—they are the cost of doing business.
The industry is moving toward a future defined by the friction between biometric security and AI-powered threats. We’ll likely see a shift toward advanced cryptographic verification and behavioral biometrics to backstop the audio. But that’s tomorrow. Today, the job is simple: harden the infrastructure you have, watch the metrics that matter, and stop assuming the voice on the other end of the line is who they say they are.